What is a Crypto Wallet?
A wallet is an app for generating, managing, and storing cryptographic keys - your public and private keys.
With a wallet, you can:
- Check your balance
- Receive funds
- And send funds
Wallets generally don’t allow you to buy cryptocurrencies; that is what exchanges are for.
All exchanges provide you with wallets to store your coins in after you buy them, but wallets usually don’t provide you with an exchange service.
A wallet:
- Generates a random private key, sk
- Derives your public key, pk, using elliptic curve cryptography
- Derives your address(es) from your public key
- Stores your private key(s)
- And takes care of signing transactions
In this article, we want to give you an overview of what types of wallets there are and help you find the right wallet for you. We show you how your mnemonic phrase is generated, and how it relates to your actual private key.
Depending on the wallet implementation, the process for generating your address from a private key looks slightly different.
How Do Crypto Wallets Work?
A wallet is a program that has three main functions:
- Generating, storing and handling your keys and addresses
- Showing you your balance
- Creating and signing transactions to send funds
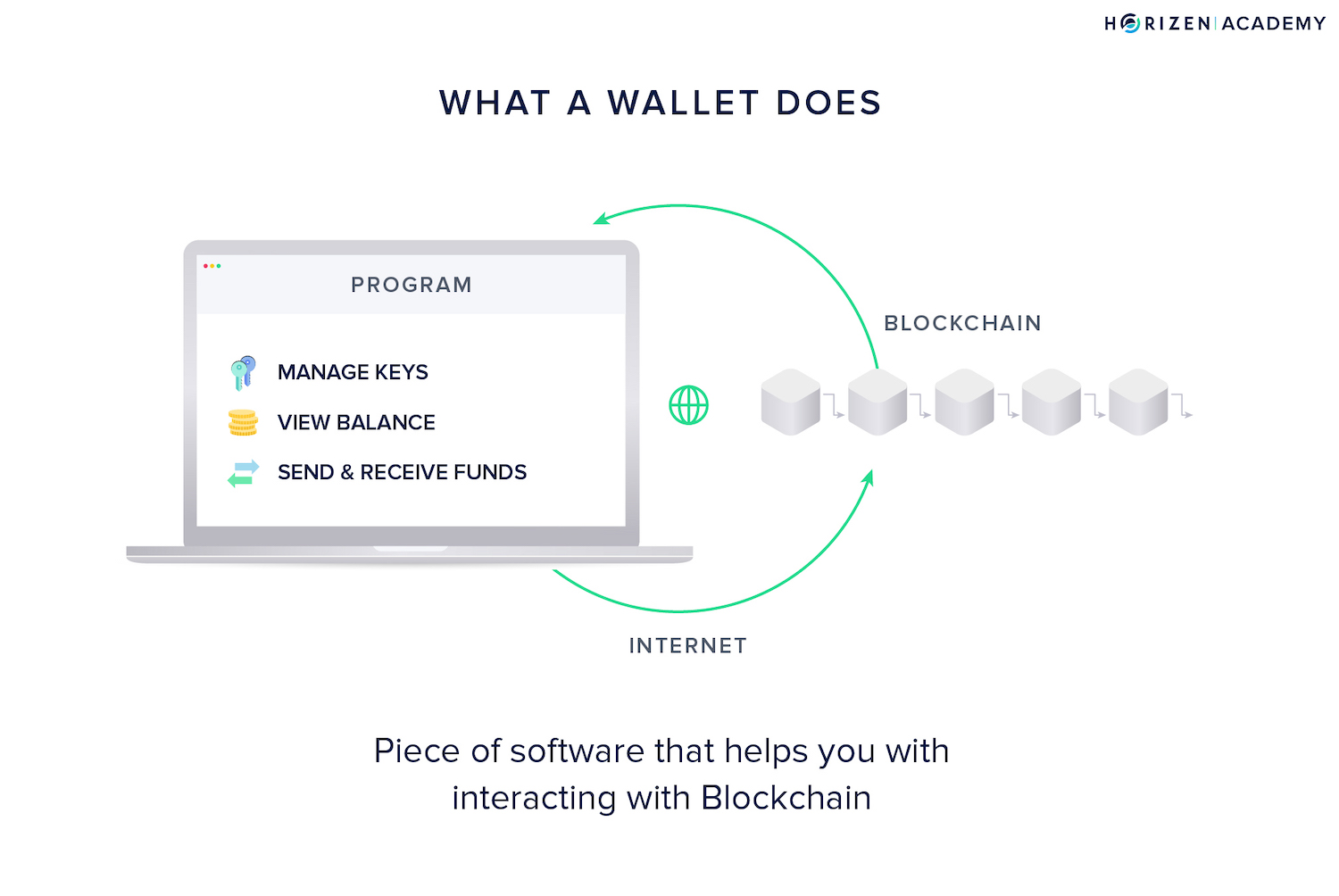
The first function is the primary function and main differentiator of all wallets: generating, storing, and handling your keys.
Having access to your private keys means being able to spend your money. Where you store your keys determines the safety of your funds and at the same time, the convenience of using them.
With wallets, there is usually a trade-off between security and convenience:
- Having some funds in your mobile wallet on your smartphone makes them easy to spend, but not very secure.
- Keeping larger amounts of money on a hardware wallet is very secure, but not as convenient when you want to spend it.
Cryptocurrency Wallets Act as a Keychain
Although the term wallet might be more intuitive, the function of a wallet is closer to that of a keychain rather than an actual wallet.
To make it crystal clear:
You don’t actually store any cryptocurrency in your wallet. You just store the keys to access them on the blockchain.
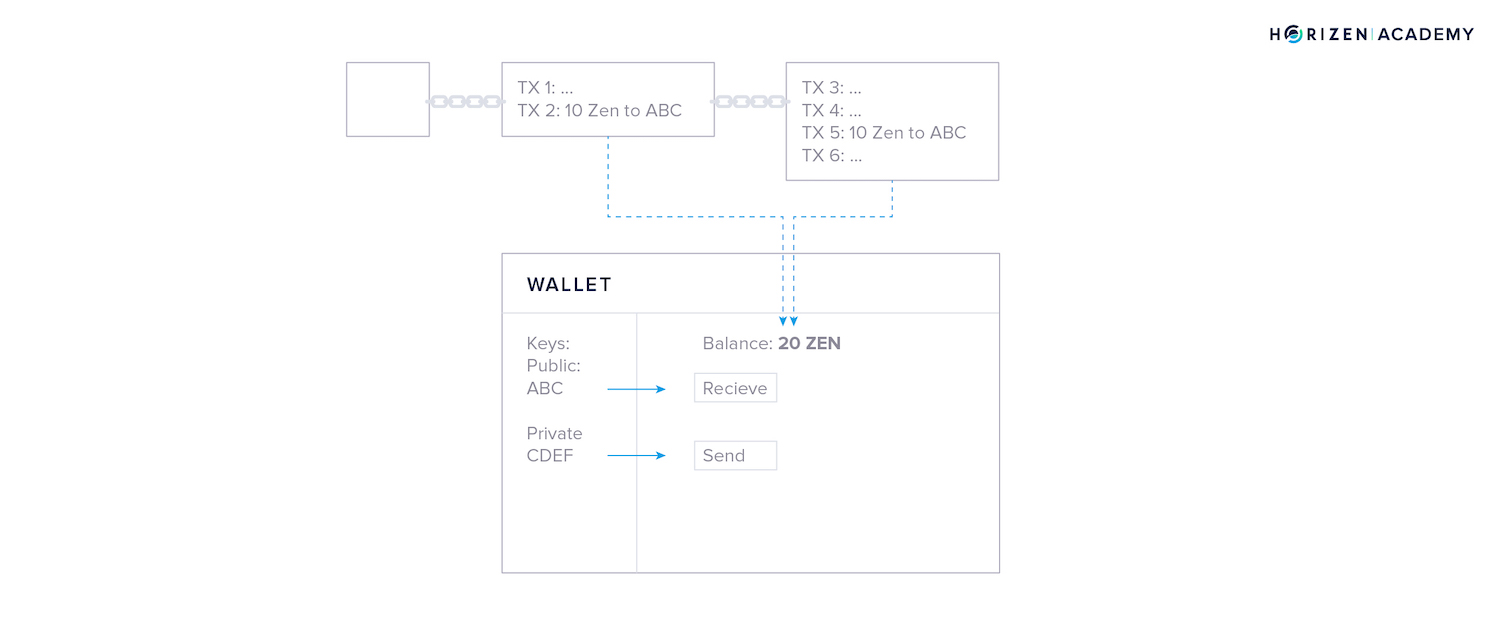
The blockchain records the amount of coins associated with a key pair, your identity on the blockchain. It calculates the amount of money the keys have access to based on all the transactions on the blockchain.
The main function of a blockchain is to store all transactions in the correct order.
If you receive 10 ZEN in a transaction and receive another 10 ZEN later on. It is clear that you, the owner of the key pair, owns 20 ZEN.
To spend your money, you need the private key stored in your wallet. This is why a keychain is a good analogy for what a wallet does.
If you don’t control your keys, you don’t control your funds.
You don’t need to understand how public-key cryptography works in detail in order to use cryptocurrencies, but the concept of your keys giving you access to your funds is still important to remember.
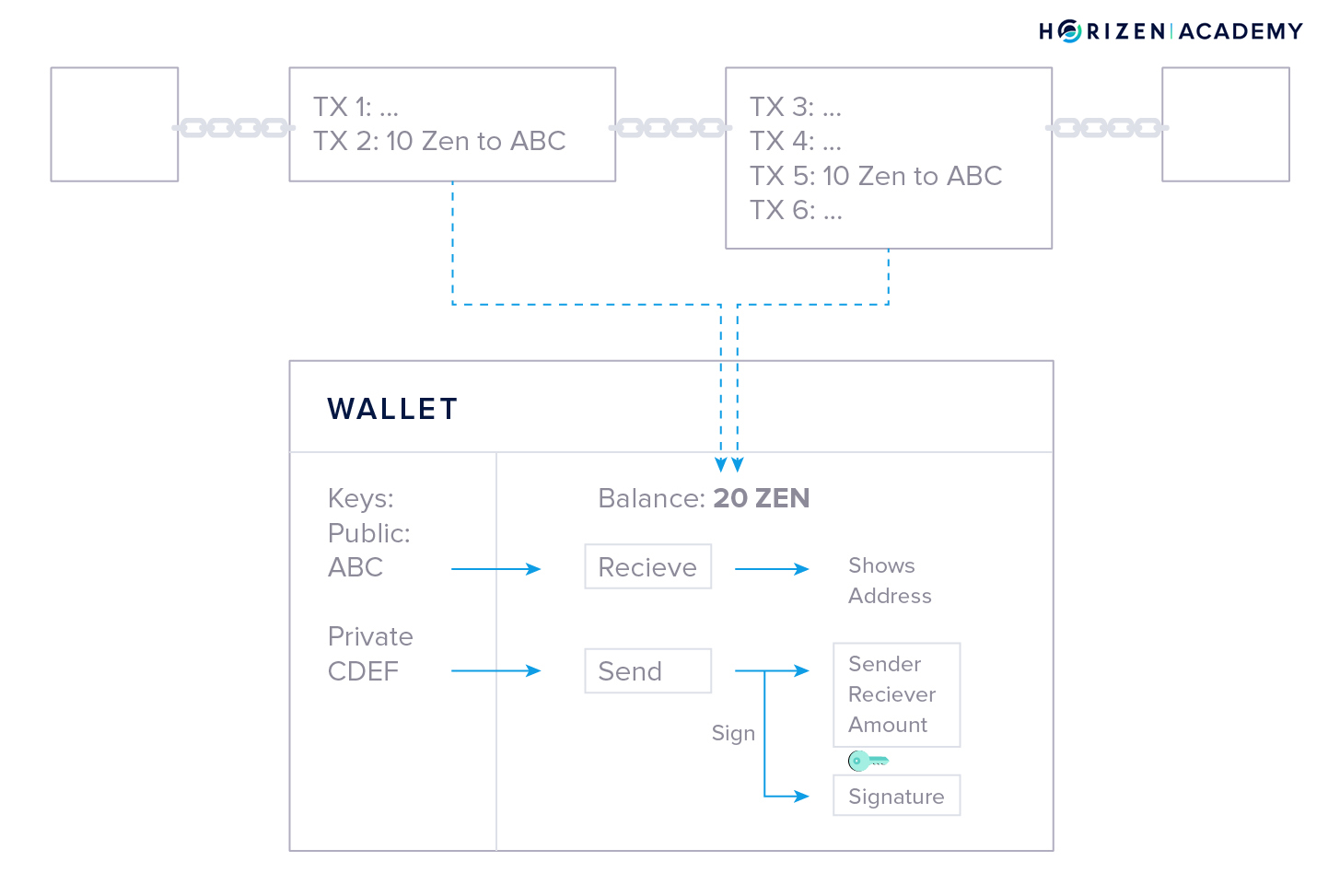
Wallets create a layer of abstraction and are becoming more and more user-friendly. Wallets show you your balance, generate an address to receive funds by just clicking “deposit” or “receive”, and provide you with a simple interface to send funds.
All you need to do is enter the address that you would like to send money to and the amount you want to transfer. The signing procedure using your private key will happen in the background when you click send.
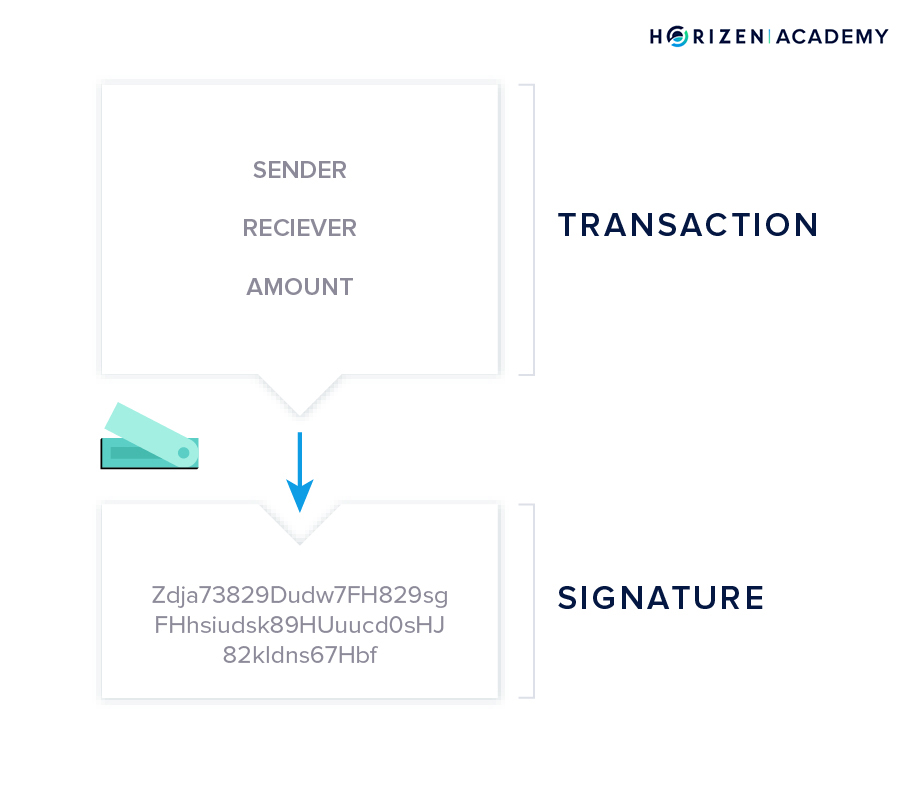
Wallet Transactions
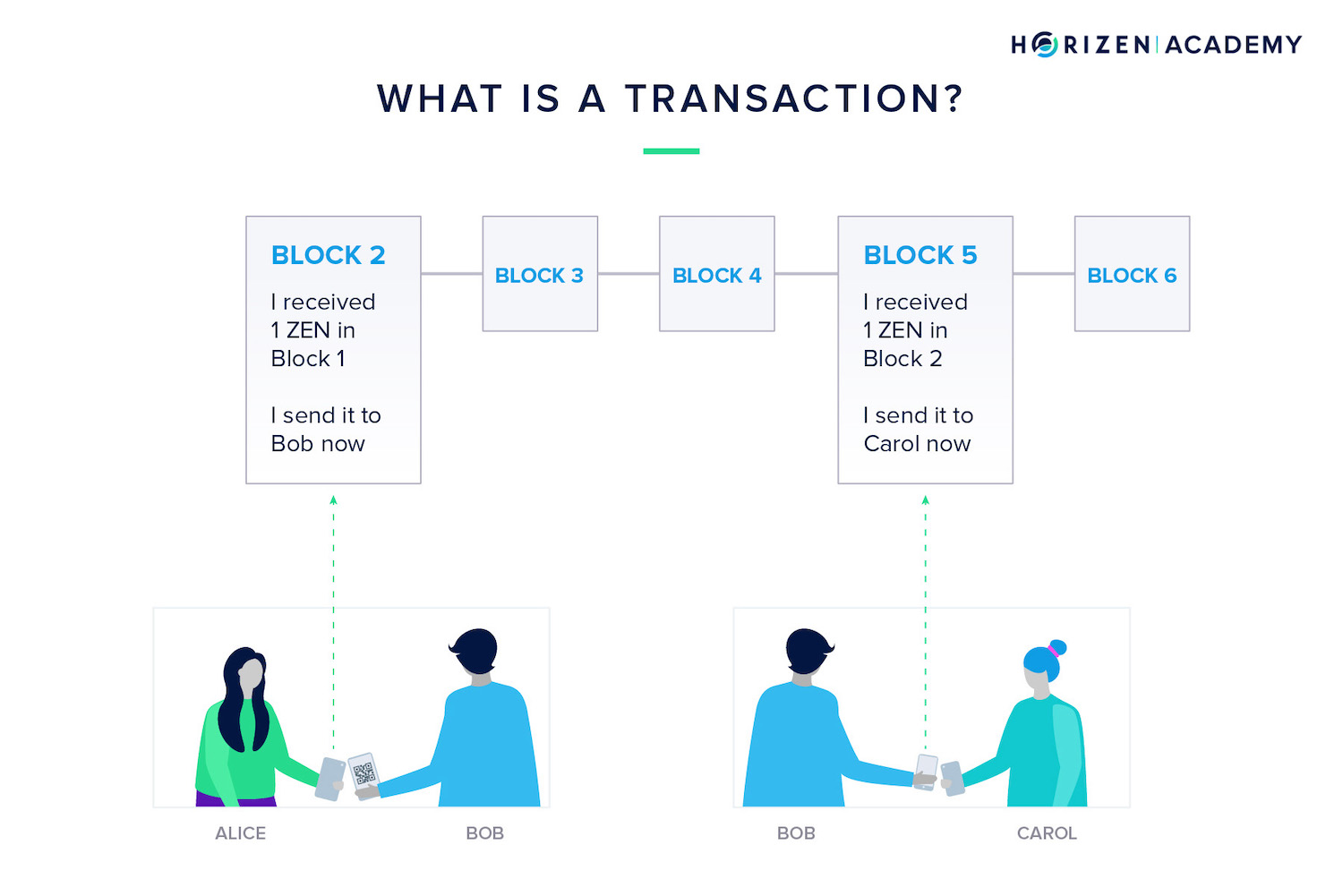
A transaction is when you send money to someone else.
When you create a transaction, you send a message to the network that some of your money now belongs to somebody else. The blockchain records this message.
For example, Alice could send one ZEN to her friend Bob. Alice will send a message to everyone on the network that she just sent Bob one ZEN.
When Bob wants to spend that one ZEN, he will create a new message to the network. This message will say: "I received one ZEN from Alice and I am sending that one ZEN to someone else now".
This is how money is sent from one person to another without the help of a central third party.
A wallet gets your balance from monitoring the blockchain for any transactions that involve your address. Initially, all transactions are cryptographically locked.
The lock is based on the address the transaction is sent to, and can only be unlocked with the corresponding private key.
Let’s assume this is your wallet:
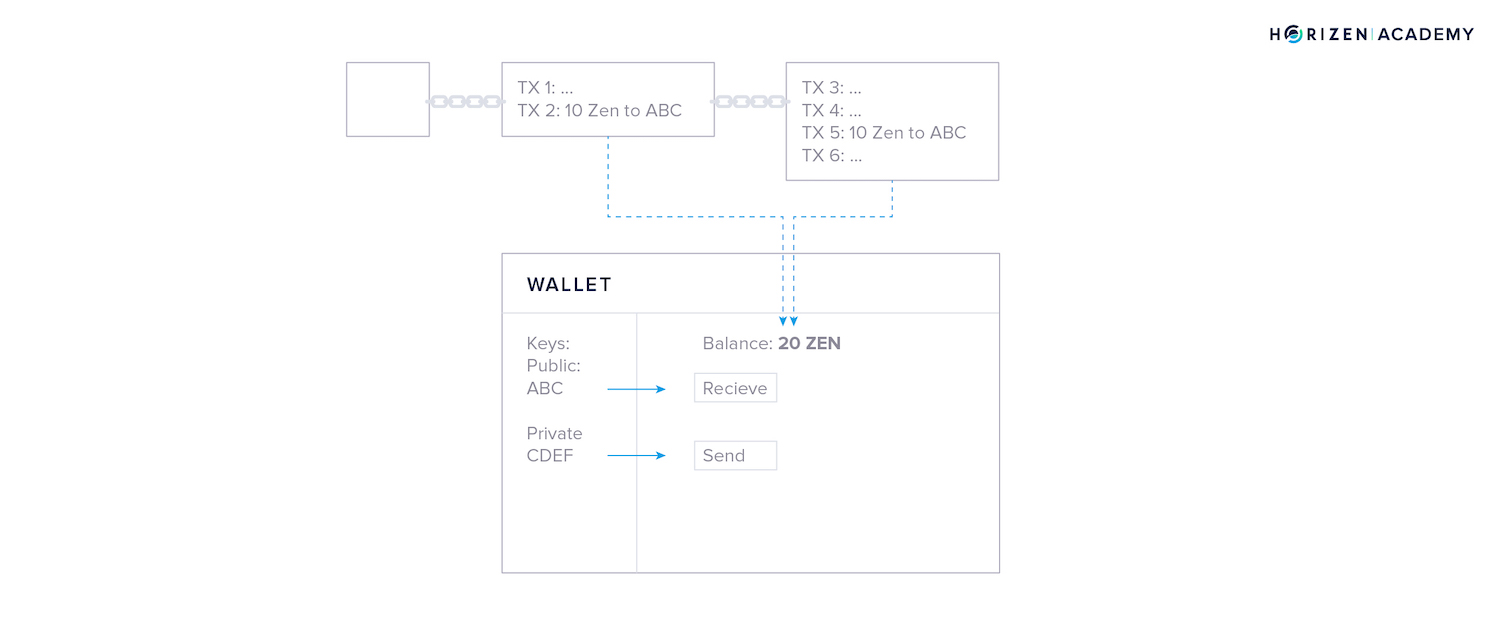
You received a total of 20 ZEN in two different transactions of 10 ZEN each. Now you want to spend 2 ZEN at lunch. Your wallet starts with a blank transaction and, in a first step, chooses one of your prior transactions to spend.
In this case, both transactions are of sufficient value, so your wallet might randomly choose the first one.
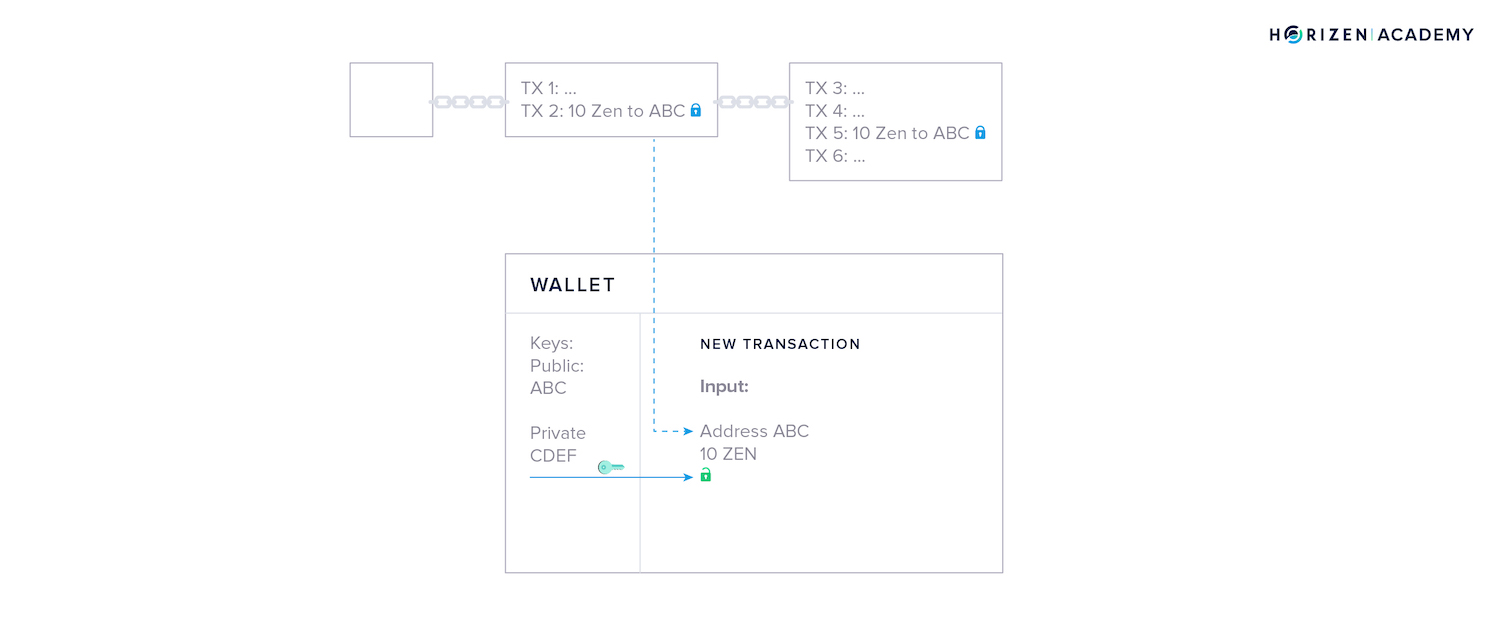
The money that is being spent in a transaction is called the input, and the money that is being received is called the output.
Your wallet places one of the outputs you own in the empty transaction and uses your private key to unlock it, so it becomes spendable - this is what we called signing the transaction.
The unlocked output is now used as an input to a new transaction.
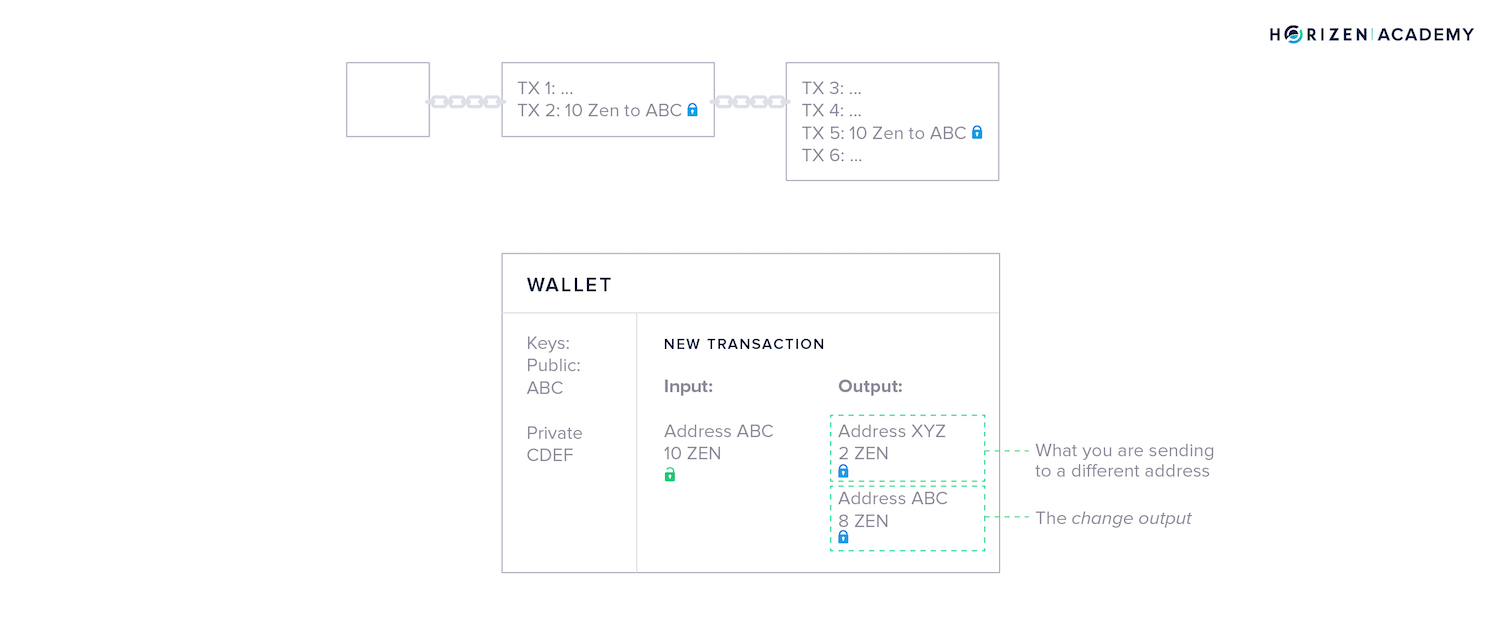
Next, your wallet creates the outputs. It asks you for an address to send money to and an amount.
You want to send 2 ZEN to address XYZ to pay for your lunch, so your wallet creates the first output accordingly.
The second output is generated automatically - its called the change output. Outputs are similar to cash denominations. If you need to pay $2 USD but only have a $10 bill, you expect to get $8 in change.
Your wallet automatically includes the change in the transaction. The newly generated outputs are locked by default.
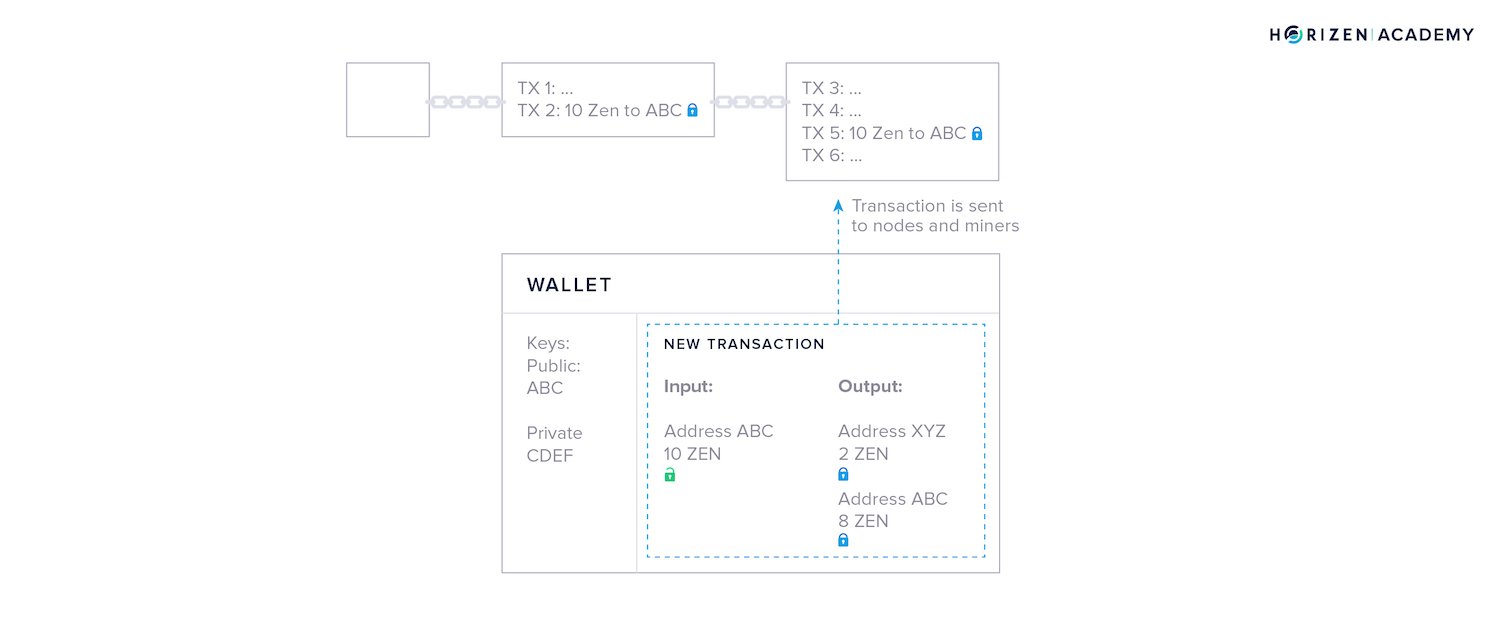
Lastly, your wallet broadcasts the transaction to the network, where all nodes and miners will verify if the signature you used to unlock your money is valid. If it is, miners will include your transaction in the next block.
The output of 10 ZEN you used is from now on publicly visible as spent. The newly created outputs of 2 and 8 ZEN are included in a new block and locked - or unspent.
Then you come across the term UTXO - Unspent Transaction Output - this is what it refers to.
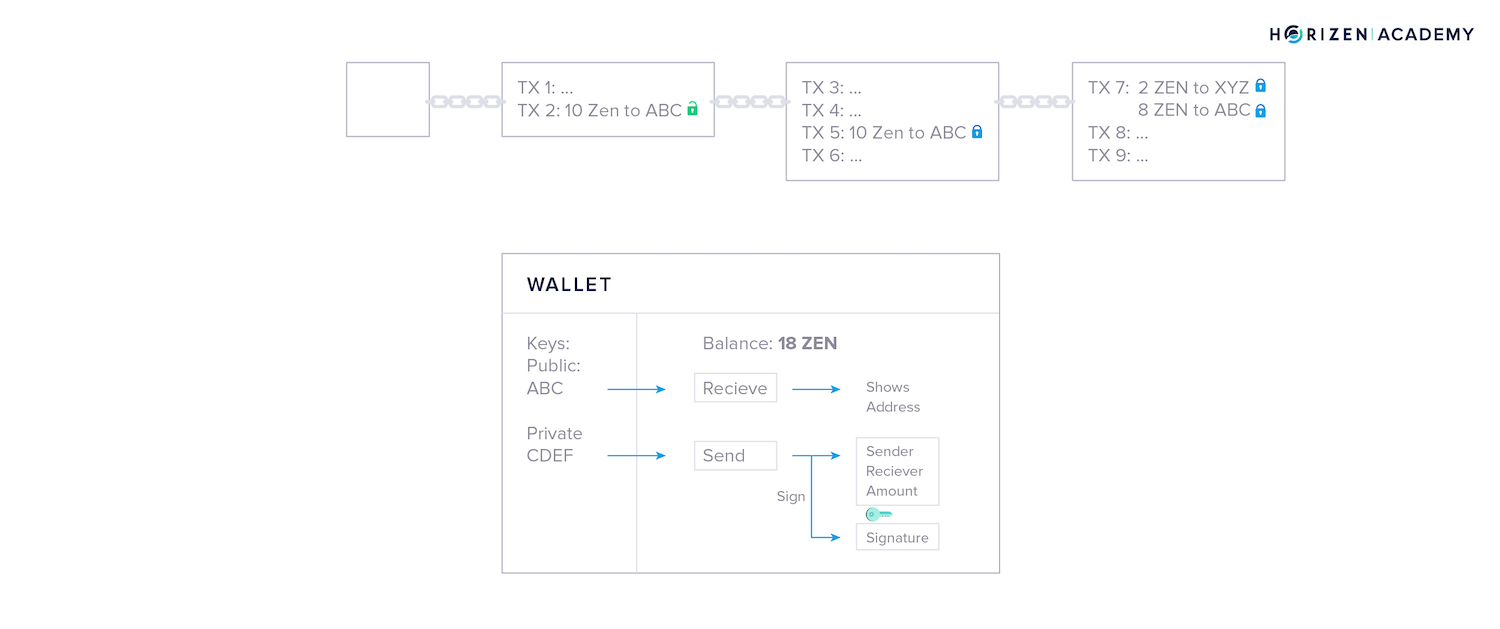
When you own 10 ZEN, it means you received 10 ZEN in a transaction, and you have not unlocked and spent that output, yet.
What if I Lose My Keys?
You don’t have to ask anybody to join the network, and you don’t have to register with a central authority to create a wallet. Being able to do this comes at the cost of you being responsible for the safety of your coins.
There is nobody that can help you recover your keys if you lose them.
If anybody were able to recover your keys for you, they would also be able to steal your funds. This would eliminate the trustless aspect of blockchains.
You may have heard stories about people searching for old hard drives because they have “lost their Bitcoins”. More accurately, they lost the keys to access their Bitcoin.
But there is a sort of recovery mechanism with many wallets called a mnemonic phrase, or backup phrase. A mnemonic phrase usually consists of 12 or 24 words. With these words, you can recover your keys. You receive your mnemonic phrase when you install and set up your wallet.
It’s essential to understand that your backup phrase is just as important as your private key itself. If anybody gets their hands on your backup phrase, they can access your money. Saving it as a screenshot or text file on your computer is not a good idea!
Types of Cryptocurrency Wallets
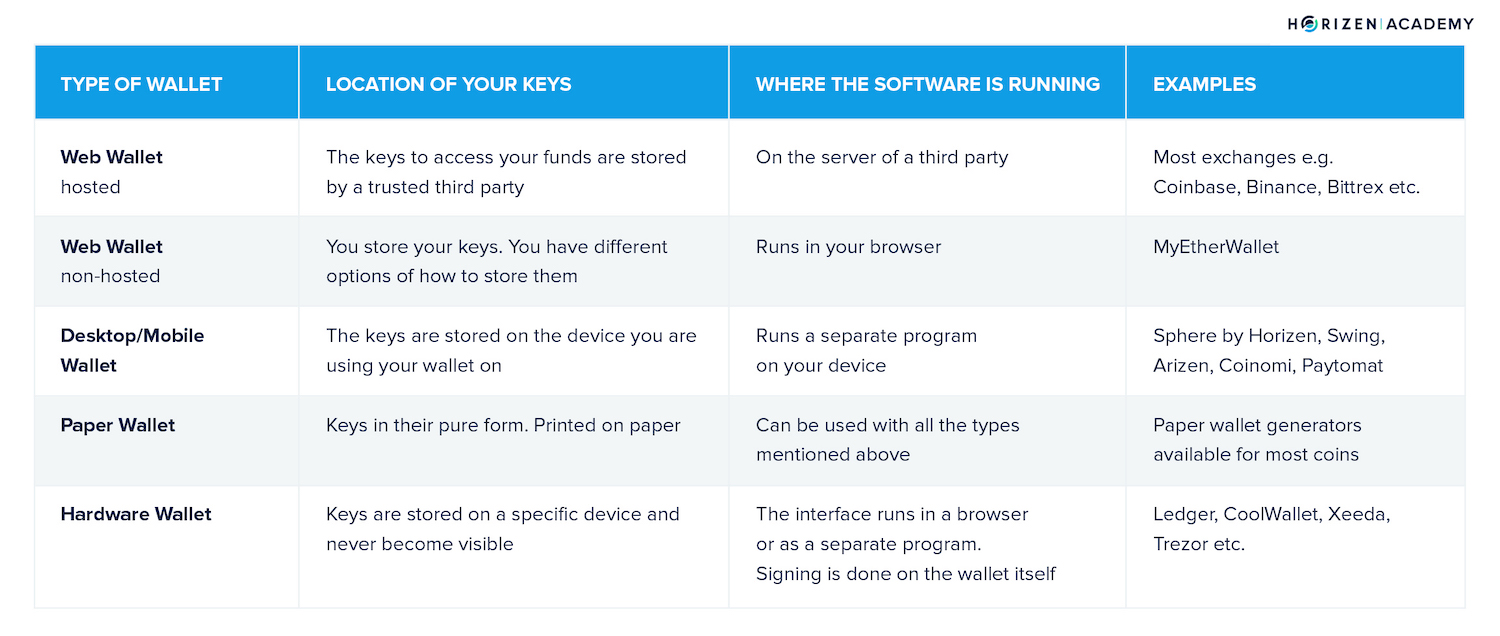
Let's take a look at the following types of crypto wallets:
- Hosted Web Wallets
- Non-Hosted Web Wallets
- Desktop Wallets
- Mobile Wallets
- Paper Wallets
- Hardware Wallets
Hosted Web Wallets
We can distinguish between hosted and non-hosted web wallets. With hosted web wallets, your keys are stored online by a trusted third party.
These parties are mostly exchanges such as Coinbase, Binance, or Bittrex. When you create an account with these entities, they will create an entry in their internal database linking your account to a set of key pairs for the different coins they have listed.
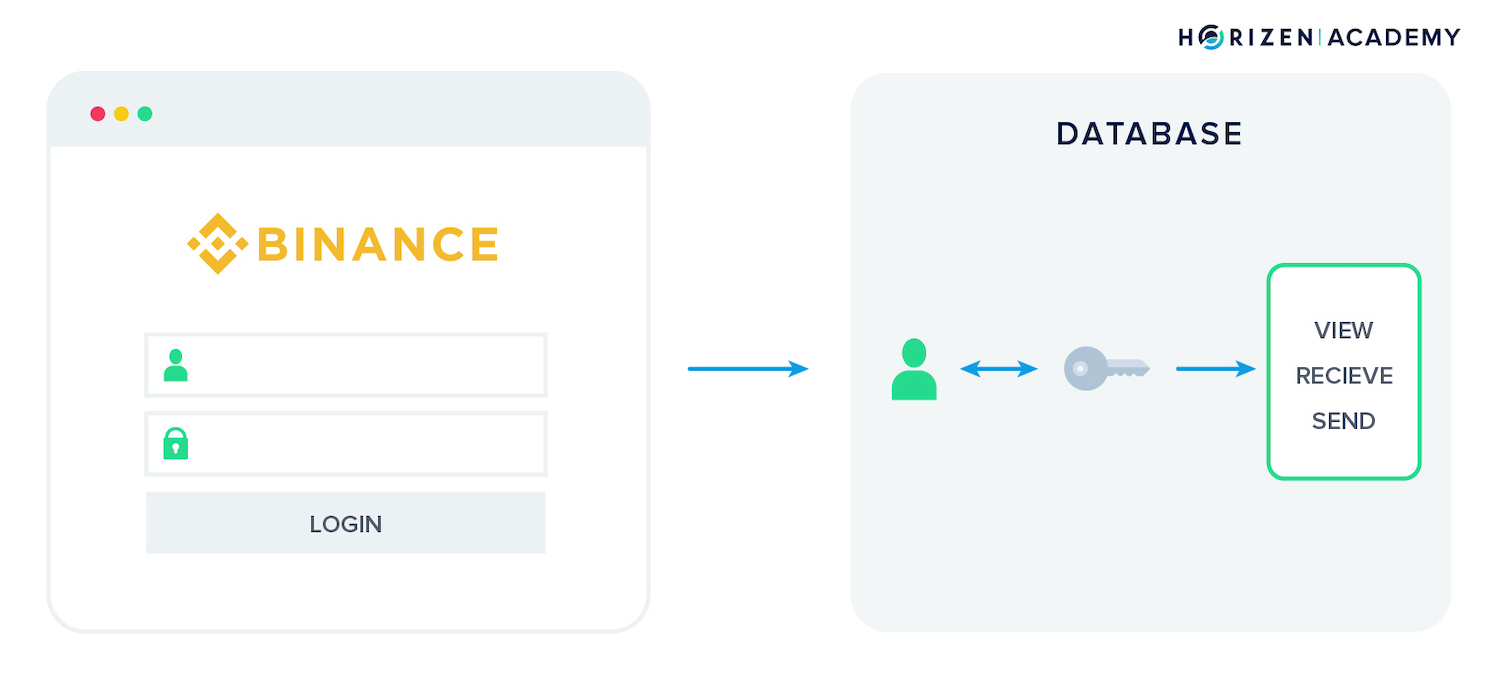
An advantage to a hosted web wallet is the option to recover your password in case you forget or misplace it. Losing your private keys, together with your mnemonic phrase, leads to a loss of funds in all other cases.
While this may sound reassuring, there are some drawbacks with hosted wallets, which are also called hot wallets or cloud wallets. Remember: if you don't control your keys, you don't control your funds.
There is always a third party risk, no matter how trustworthy the party might seem.
First, they are a more attractive target for hackers than individuals because their honeypot is much bigger.
Second, a sudden change in regulation might not allow them to allow you to withdraw your funds in a worst-case scenario. It is unlikely, but definitely not impossible.
Third, there is always a chance of an entity going bankrupt or stealing money. With major exchanges like the ones mentioned above, this risk seems small, but it does exist. Just ask former Mt. Gox customers.
For these reasons, we advise everybody to store the keys to their funds themselves. This means storing them in a wallet where you have control over your private keys.
There is a responsibility that comes with being in charge of the safety of your funds yourself, but enabling you to do this is one of the main motivations for the existence of cryptocurrencies!
You will need to keep some funds on an exchange if you plan to trade often.
Non-Hosted Web Wallets
Besides hosted web wallets, there is also a range of non-hosted web wallets. One of the most popular non-hosted web wallet is likely MyEtherWallet, which can store Ether (ETH) and all ERC-20 tokens, tokens that are "living" on the Ethereum blockchain.
These wallets provide an interface to check your funds or create transactions in your web browser, but you have to provide the keys with each login.
There are a range of options to access your wallet with MyEtherWallet, often abbreviated as MEW. The first option requires your address, but only lets you view your funds.
MetaMask is a browser plugin that provides the option to make ETH payments within your browser and the ability to login to MEW. It also provides a function detecting phishing sites and warning you when you are about to open one.
The following options, Ledger Wallet, Trezor, Digital Bitbox, and Secalot are hardware wallets. We will get to those later in the article.
Accessing your wallet with a keystore, or .json file, is possible, but not recommended. The file contains your private key, when you create your wallet, you have the option to download it. If it gets into the wrong hands, they will have access to your funds, so saving it on your desktop is not the ideal solution.
If you want to use this method, you should encrypt the .json file and store it on a separate device like a USB drive. To use, connect the drive, decrypt the file, then select the file in your browser and voila. After that, you can disconnect your storage medium of choice again.
The last two options are more or less the same with regards to safety. You can either enter your private key directly or your mnemonic phrase, which yields your private key when hashed, which are both problematic if your machine is compromised.
In conclusion, a non-hosted web wallet is quite convenient and just as secure as the method you choose to provide your keys with.
Desktop Wallets and Mobile Wallets
If you start off with the question "where are your keys?", the desktop and mobile wallet will give you the same answer: on the device.
Phones and tablets are more powerful than ever, the difference between a desktop and a mobile wallet is marginal. It is also arguable whether one is safer than the other.
If you want to use crypto for everyday transactions, there is almost no way around keeping some funds in a mobile wallet.
As mentioned before, when creating your wallet, you will get a mnemonic phrase that you should keep safe. Usually, there is a PIN, password or Face/Touch-ID protection to access the wallet.
You should never keep more funds in a mobile wallet than you are willing to lose.
It's the same as with cash: you don't carry around all your money in a wallet. You withdraw as much as you are comfortable handling in cash and keep the rest in your account or under the mattress.
With desktop and mobile wallets, there is a choice between single and multi-currency wallets. Those should be rather self-explanatory terms. The former allows you to store one coin, while the latter supports multiple currencies.
Some of the more popular examples of desktop wallets include Coinomi and Sphere by Horizen. For mobile, there are Mycelium or Paytomat, just to name a few.
If you get your first coins on an exchange, I would recommend you transfer your funds out of the exchange from the hosted web wallet, onto a desktop, paper, or hardware wallet.
Send a fraction first to make sure everything works as planned.
If your first transaction works, then you can send the rest. You are now protected from third-party risk, but have full responsibility for your funds yourself.
Paper Wallets
Referencing our golden thread again and asking "where are the keys" gives you a simple answer with a paper wallet: in your hands!
A paper wallet is your public and private key pair printed on paper. Almost every cryptocurrency offers a paper wallet generator.
To create a key pair, you generally first have to create some entropy, a term for disorder. In other words: you want your keys to be as random as possible.
This is mostly done automatically, but sometimes you will find features where you have to randomly move your mouse or hit keys on your keyboard to create randomness.
When printing your paper wallet, you should not use a shared printer, like the one in your office. In a best-case scenario, the printer doesn't even have an internet connection. Printers usually keep a copy of the files they printed last, and an attacker might exploit this.
You will end up with something looking like this after printing the wallet.

There is only one thing left to do: send your coins to the public key. After that, you have a perfect long term storage solution for your coins.
The main risk with a paper wallet is you actually losing or destroying the wallet by accident. If you don't have a mnemonic phrase to recover the private key, you are at risk of losing all funds on the wallet.
So choose wisely where to store your paper wallet. Print several copies if you feel uncomfortable having only one and store all of them in separate, safe places.
Hardware Wallets
Moving on to everybody's darling: hardware wallets.
With a hardware wallet, your keys are stored on the device in something called the secure element. The secure element is a place to store data, in this case your keys, that cannot be directly accessed by your computer or any other device even when it is connected.
Although it does look like a simple USB drive, it can actually do more than just providing storage for your keys. To use a hardware wallet, you usually have a few options of which interface to use.
Like MyEtherWallet, a few other wallets offer hardware wallet support. Additionally, you have the native wallet apps provided by the producer. In the case of Ledger, for example, the native app is called Ledger Live.
How Does a Hardware Wallet Work?
The interface generates an address when you want to receive funds.
Using this feature is pretty straightforward: if you click the receive button, the process runs in the background and the address is displayed for you to share with the sender.
If you want to send money, the app creates the raw transaction that needs to be signed. The unsigned transaction is now sent to your hardware wallet, where it gets signed with your private key.
The signature is then returned to your computer and the complete transaction, including the signature, is broadcasted to the network.
Your private key(s) do not leave the device, so they are not visible to the computer you are using your hardware wallet with at any time. This is why a hardware wallet is considered the most secure way of storing crypto, especially large amounts.
If your device ever breaks, you have your mnemonic phrase as a backup. At the risk of being repetitive: your mnemonic phrase, under all circumstances, must stay private and in a secure location.
A copy at a trusted family member or in a bank vault might be a good idea in case of a fire or flood.
Summary - Crypto Wallets
A wallet is a program that helps you manage your keys and create transactions easily. Your wallet looks at the blockchain to determine how much money you own by reviewing the transaction history. To send funds, it writes a transaction and signs it, meaning the wallet encrypts it with your private key
There are many ways to store your cryptocurrencies. Usually, there is a trade-off between convenience and security. The most important question is: where are the keys?
A wallet is only a piece of software, an interface, that helps you perform the basic functions of cryptocurrencies: view your balance, create an address to receive funds, and create transactions to send funds.
With a hosted online wallet you are trusting a third party to handle your keys. You have the option to recover your password if misplaced, but there is always a significant third-party risk.
If you don’t control your keys, you don’t control your funds!
With desktop, mobile, paper or hardware wallets you own the keys and nobody but yourself is responsible for keeping them safe. If your device breaks you have a mnemonic/recovery phrase to recover access to your money.
The mnemonic phrase is a list of words that can be used to restore your private key. The mnemonic phrase is as sensible as your private key itself and if it gets in the wrong hands, your money can be stolen. This should not scare you, but make you cautious.